In recent years, Suzhou Image Company has continued to invest in research and development in IDs and document anti-counterfeiting. We have noticed that some companies, organizations, and even governments have been troubled by counterfeit ID cards and documents, which has even caused a certain degree of economic losses. Using holographic security technology is a very effective way to combat fake IDs.
The previous article introduced the importance of comprehensive security features in ID card security. Today, we will focus on the application of optical holographic technology in cards.
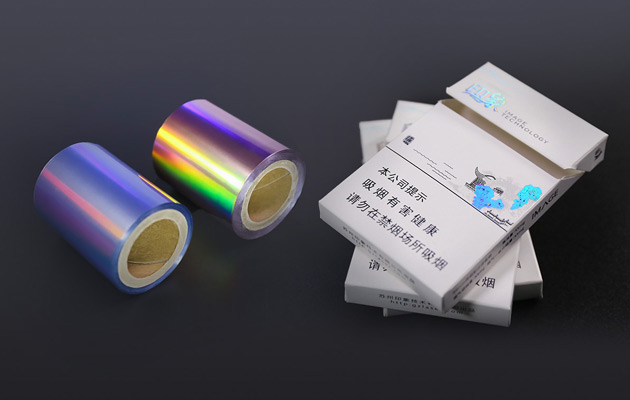
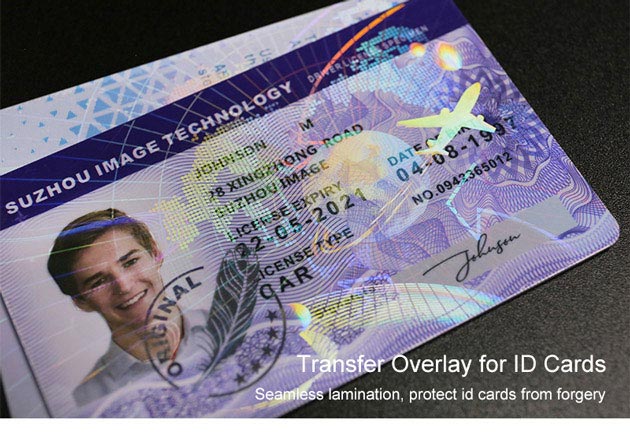
There are two processes for applying optical technology to cards, one is holographic lamination, and the other is hot stamping. For more details, please click Three Security Features to Safeguard Your ID Card from Threats.
The use of optical security technology on the card not only enhances visual security, making it more convenient to verify; on the other hand, it can provide physical anti-counterfeiting protection, deter counterfeiters through complex optical technologies, and ensure the security of personal information.
Suzhou Image Technology is a high-tech enterprise with rich experience in the field of ID cards and documents anti-counterfeiting. We not only provide holographic ID overlays, hot stamping foils for ID cards, laminators, and printer ribbons, but we can also provide finished security ID cards.
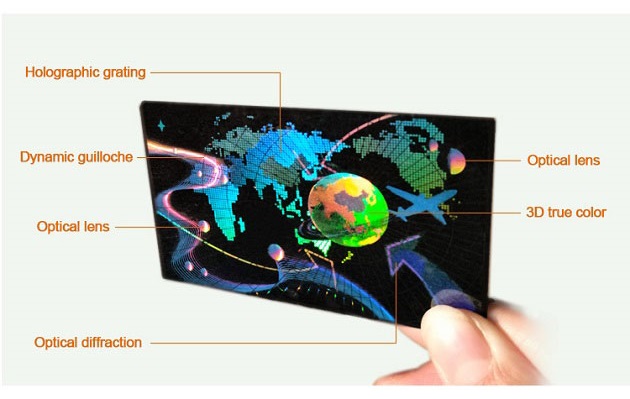
At present, our company has independently developed more than twenty optical holographic technologies, which are divided into overt, covert, and forensic security features.
These security elements can be applied to ID cards to increase the threshold for forgery, making it very difficult to forge, thereby making your ID cards more secure. If you are not familiar with these optical techniques, our team will help you understand which one is best for your requirements.
Security ID Cards with Overt Visual Verification
The overt technology is notified in public description documents, publicity materials, and other media. It can usually be identified with the naked eye and is not affected by the identification personnel, identification tools, and environment. Below is their detailed description.
Rainbow Hologram

Rainbow color, wider viewing angle under point light source, and has a stable color and presents beautiful and dynamic color change. The rainbow hologram is a type of overt anti-counterfeiting technology that will make your ID cards more attractive and shiny.
2D/3D
2D /3D optical hologram technology is often applied to various ID cards to offer visual security. It consists of more than two layers of planar images, forming a 3D scene. When viewed with the naked eye, it feels that the flat graphics form a depth of field (or floating) of 2 to 5 mm.
True Color
True color 2D/3D is a plate-making technology that uses a computer to position and combine three space-frequency gratings to restore RGB color images. For example, reproduce the true colors of the original object under a specific angle, e.g. portrait, blue sky, and white cloud. actual effect.
Shallow Structure Lens
Shallow Structure Lens is also called the color cat eye; it can present a high gloss lens effect.
Metal Relief
A full view field relief effect, non-rainbow color, single metal gloss
Zero Level Light Diffraction

A transparent hologram with stable color changes under reflected light angle or a metalized hologram with hidden graphics under a big view angle. Please have a look at this overlay, it has stable color change between red and green when rotating 90 degrees. The holographic grating is commonly used for sensitive documents, driving licenses, and National IDs, it’s very hard to do forgery.
Flip-Flop
Flip-flop hologram technology is a perfect combination of visual appeal and security performance. You can view different graphics at different angles in the same position while rotating the hologram image.
You will observe two graphics “TULEN” and “ORIGINAL” exchange when rotating the sticker. The flip flop is very difficult to copy, normal printing technology makes it impossible to realize the same effect.
Optical Guilloche
0.3mm~0.1mm width thin line with dynamic effect. This is the thinness and dynamic design that cannot be achieved by printing.
Embedded Super Thin Metal Logo Label for ID Card Lamination
It is a micro-nano optical hollow metal logo, mainly used for card lamination, which can improve the texture of the card. It is mostly used for VIP cards, credit cards, club membership cards, etc.
Suzhou Image has its own YouTube channel, and there is a playlist specially for various holographic security technologies, if you are interested in these security features, click Optical Technologies for more details.
Security ID Cards with Covert Security Features
Covert optical technologies are usually used for high-level security projects, it’s only for the internal management and inspection needs of manufacturers and users and does not publicize and inform the public.
There are certain requirements for identifying personnel, identification tools, and the environment. Microscopes, laser pointers, ultraviolet lamps, polarizers, magnetometers, code scanning, and electronic chip scanners are used for professional anti-counterfeiting inspection and recognition.
Special detection films, decode chips, detectors, special APP reading software, and other special devices to carry out security inspection and recognition.
Micro Graphics (Micro Text)
Text or LOGO images with a height of 50μm~100μm. It requires a 50-100 times handheld magnifier to observe the miniature information. Do you notice some lines like an earthworm in the sticker, that is micro text. Continuous “Guarantee” can be seen clearly under 40×magnifier.
Information Fiber (Fiber Line)

Similar to random fiber lines on banknotes and counterfoils, one can recognize the hidden information on the fiber line with a 40-times magnifier.
Pixel Character (Pixel Dot Matrix)
Pixel character is an encryption technology made by a dot-matrix system. You will observe each pixel in the image is formed by a specific graphic or letter (such as a regular five-pointed star) under 80 times magnifying glass.
Each pixel consists of one more multi-character unit, often hidden in a diffractive optically variable image device (DOVID).
Laser Re-production (Hidden Text)
Use a laser pointer to recognize the hidden information, present two-directional symmetric or two-directional different static graphics, and also can be designed as projection animation. Use a small laser pen to shine on the hidden area, it can show out the hidden graphics, for example, the OK” word.
Moiré Encryption
A dedicated decoder chip will be placed on the sample, and the rotation decoder chip to a certain position should see the invisible text display.
Diffraction Characteristic Graphics (Mobile Re-production)
Use mobile light or other point light sources, present specific diffraction graphics, and read the graphics on the mobile screen. Also can scan with a specialized mobile APP to authenticate, and link to a cloud database for track and trace.
Security ID Cards with Forensic Security Features
Only a few designers or users know it and usually take appropriate security and confidentiality measures for final authentication such as arbitration identification, proof, and decryption.
It should be certified by a third-party testing agency with relevant testing qualifications. Use a metallographic microscope, confocal microscope, SEM scanning electron microscope, atomic force microscope, etc. for inspection and analysis, and issue a third-party identification report.
The above is just a part of our numerous holographic anti-counterfeiting technologies. If you have any interest in identity solutions, please send your specific requirements and our team will provide you with appropriate and unique solutions.